Android Advanced Flow and the Formalisation of Sideloading
Google is implementing "Advanced Flow," a security framework that introduces a mandatory 24-hour delay and identity verification for sideloading applications (Ars Technica, March 2026). While marketed

The Pitch
Google is implementing "Advanced Flow," a security framework that introduces a mandatory 24-hour delay and identity verification for sideloading applications (Ars Technica, March 2026). While marketed as a defense against high-pressure social engineering, it effectively shifts Android toward a closed-garden model by requiring developers to provide government IDs to remain "verified."
Under the Hood
The mechanism forces a 24-hour waiting period before a user can install an unverified APK, purportedly to allow time for "security reflection." To bypass this or distribute apps without the delay, developers must pay a $25 fee and submit their legal name, home address, and a government-issued ID (KeepAndroidOpen.org).
The technical friction extends to the device state itself. Users wishing to bypass these safeguards must keep "Developer Mode" active, a state that frequently triggers "Strong Integrity" failures (PCMag). In practice, this means many banking and high-security enterprise applications will refuse to execute, forcing a binary choice between sideloaded software and financial access (HN Thread).
Current limitations and technical impacts include:
* Broken CI/CD pipelines for QA teams needing immediate deployment of test builds (Dev.to).
* Privacy concerns regarding the centralized storage of global developer home addresses (Reddit r/privacy).
* A 20-device cap for "limited distribution" accounts intended for students and hobbyists (Thurrott.com).
* Potential for Google to act as the sole arbiter of software distribution on "certified" hardware (The Register).
We do not know yet which specific enterprise apps will implement hard blocks once the requirement is enforced. Furthermore, Google has not disclosed how they will handle ID verification in jurisdictions with limited government infrastructure (UsedBy Dossier). The rollout begins in Brazil and Southeast Asia in September 2026, with a global mandate following in 2027.
Marcus's Take
This is a calculated ecosystem lock-in disguised as a security patch. By tying sideloading to Developer Mode—and thus breaking banking app compatibility—Google is making third-party distribution socially and practically impossible for the average user. If your organization relies on sideloading for internal tools or rapid QA, you have eighteen months to migrate to a formal enterprise distribution channel or a private Play Store repository. The "Open Handset Alliance" is officially a historical footnote.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
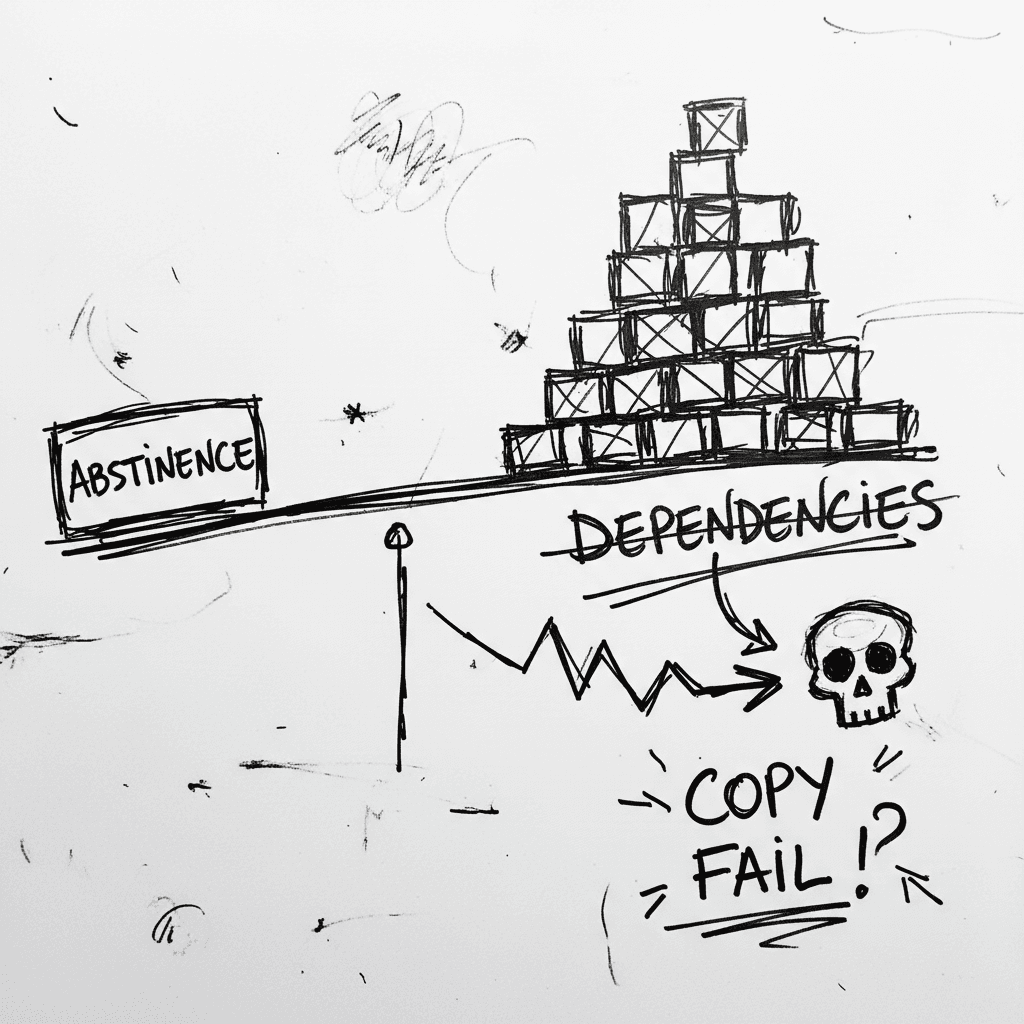
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
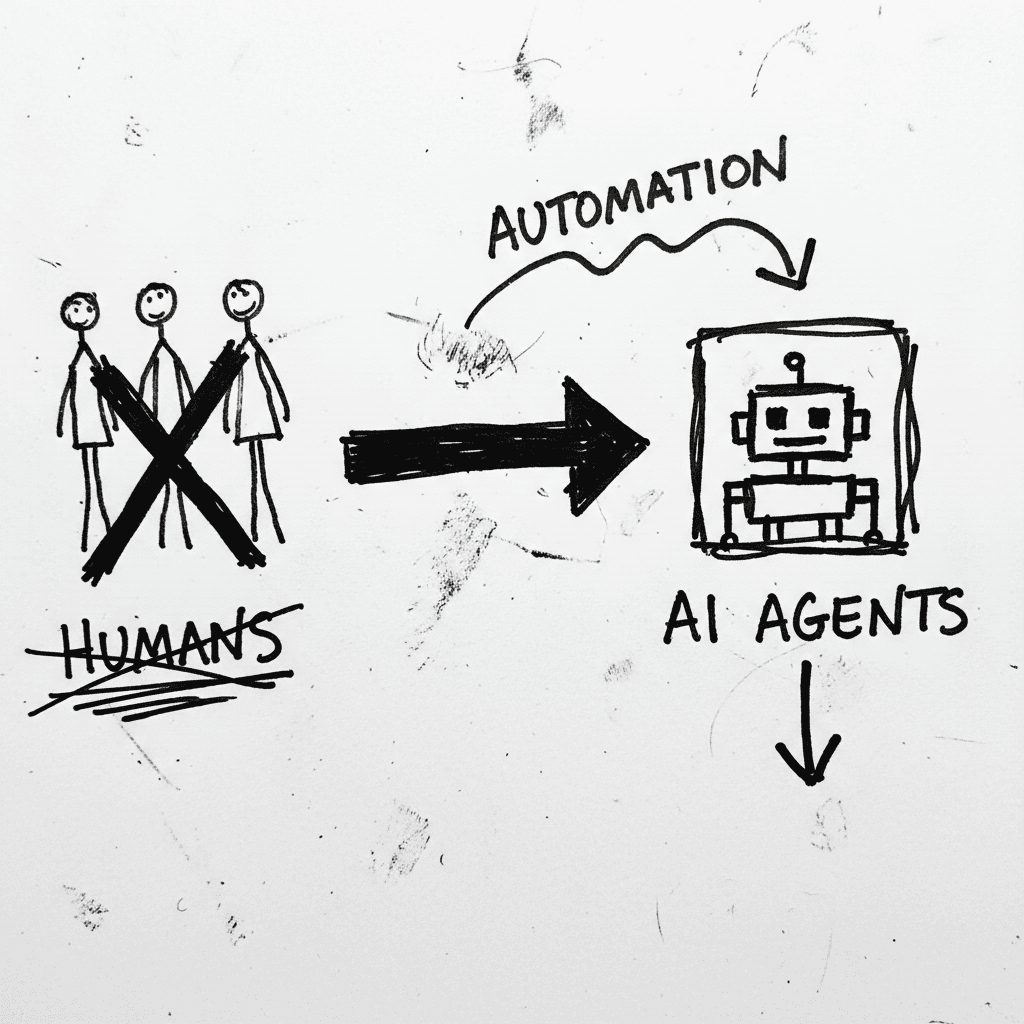
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
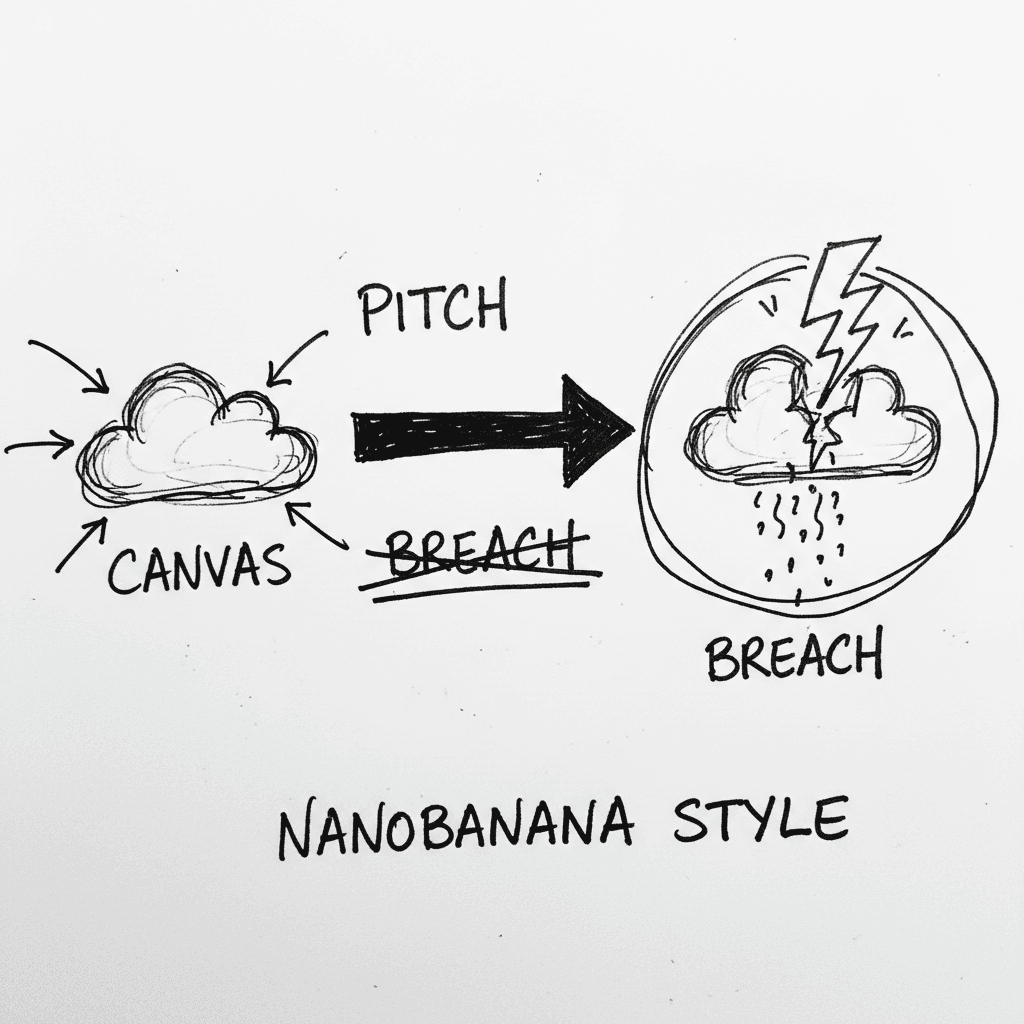
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.