Google Workspace CLI: Rust-based MCP Integration for AI Agents
The lack of official support means there is no service-level agreement for breaking changes in the pre-v1.0 phase. We don't know yet how its rate-limiting logic compares to Enterprise-grade tools like

The Pitch
The Google Workspace CLI (gws) is an experimental tool built in Rust that prioritises "Agent DX" over human readability. It provides a Model Context Protocol (MCP) server designed to give LLMs like Claude 4.5 Opus and Gemini 2.5 direct, structured access to Workspace APIs (GitHub).
Under the Hood
Version 0.4.1 leverages the Google Discovery Service to dynamically generate commands for Gmail, Drive, and Calendar (GitHub Releases). Unlike traditional CLIs that focus on pretty-printing for humans, gws generates deterministic JSON payloads optimized for LLM inference and tool-calling (poehnelt.com).
The technical implementation via Rust ensures low-level efficiency, but the operational requirements are significant:
* Lead contributor Justin Poehnelt has designed it for the Model Context Protocol (gihyo.jp).
* It functions as a plugin for Gemini 2.5 and Claude 4.5, allowing agents to browse files or draft emails via structured tools (UsedBy Dossier).
* Authentication requires manual creation of a GCP project and OAuth 2.0 Client ID configuration (HN Comment 5).
* Security remains a bottleneck, as the tool requires high-privilege OAuth scopes and local management of refresh tokens (toriihq.com).
* It is explicitly labelled as "not an officially supported Google product" (GitHub).
The lack of official support means there is no service-level agreement for breaking changes in the pre-v1.0 phase. We don't know yet how its rate-limiting logic compares to Enterprise-grade tools like GAM, nor do we have a public roadmap for native Gemini 2.5 integrations beyond the MCP server (UsedBy Dossier). Setting this up is a manual chore that would likely baffle anyone without a background in GCP IAM.
Marcus's Take
Play with this in a sandbox, but keep it far away from your production environment. The "Agent-first" design philosophy is logically sound for 2026, yet the security implications of local token storage for high-privilege AI agents are a massive liability. Unless you enjoy explaining to your CISO how a rogue local process exfiltrated the entire Drive via a v0.4 experimental binary, stick to official SDKs for critical automation.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
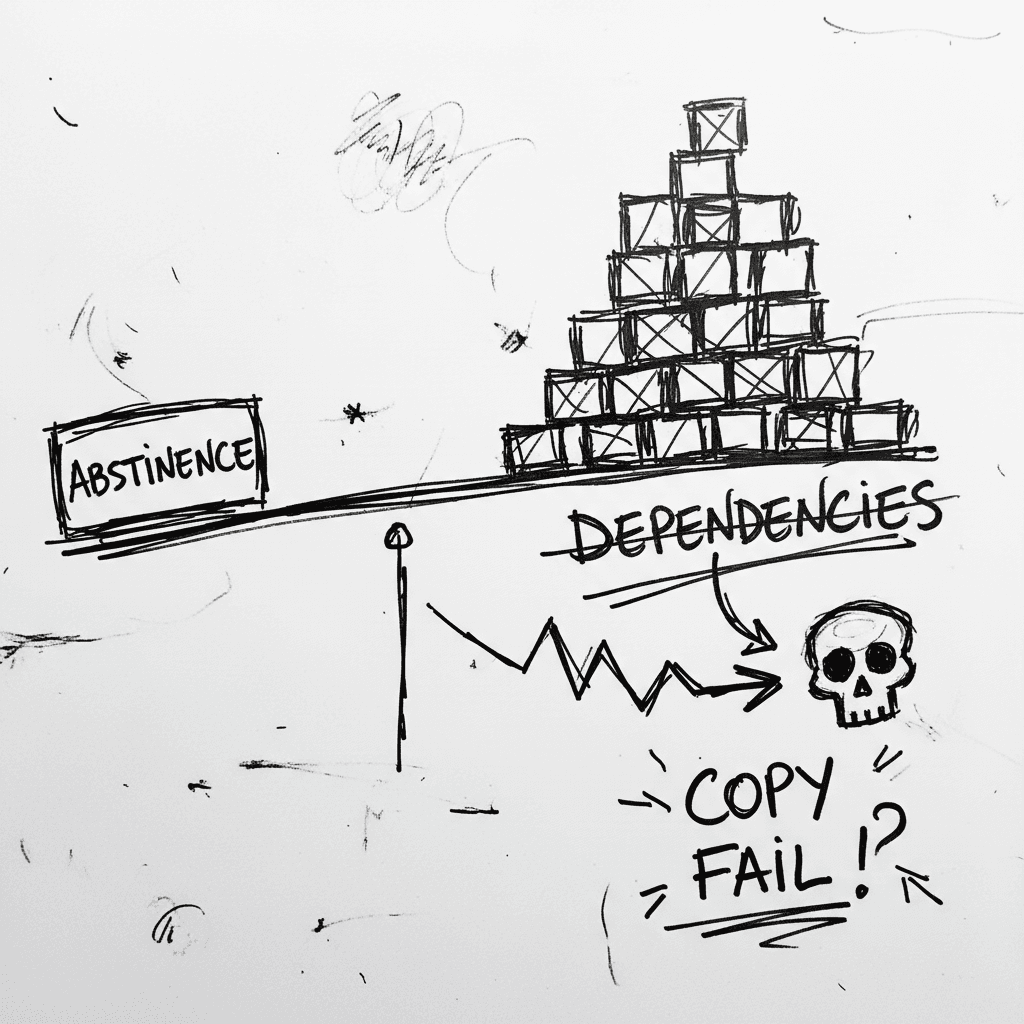
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
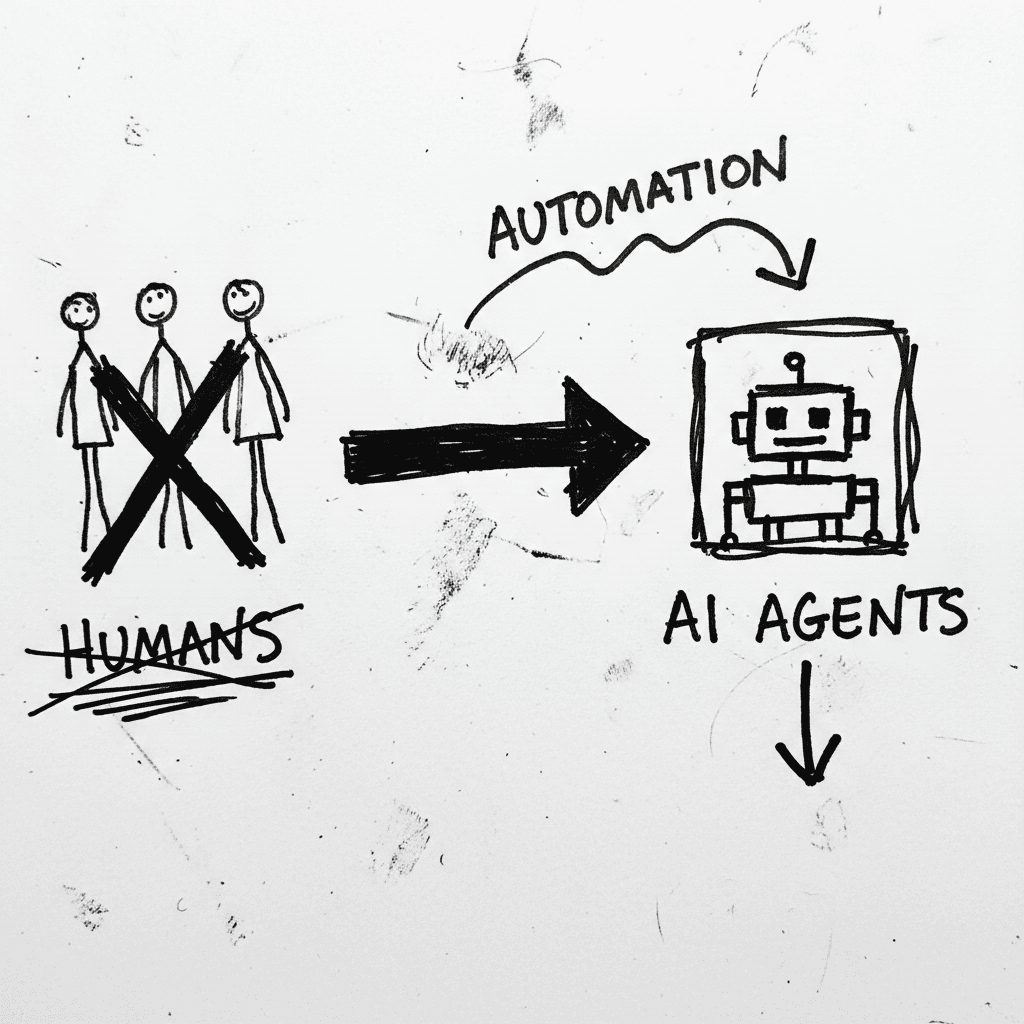
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
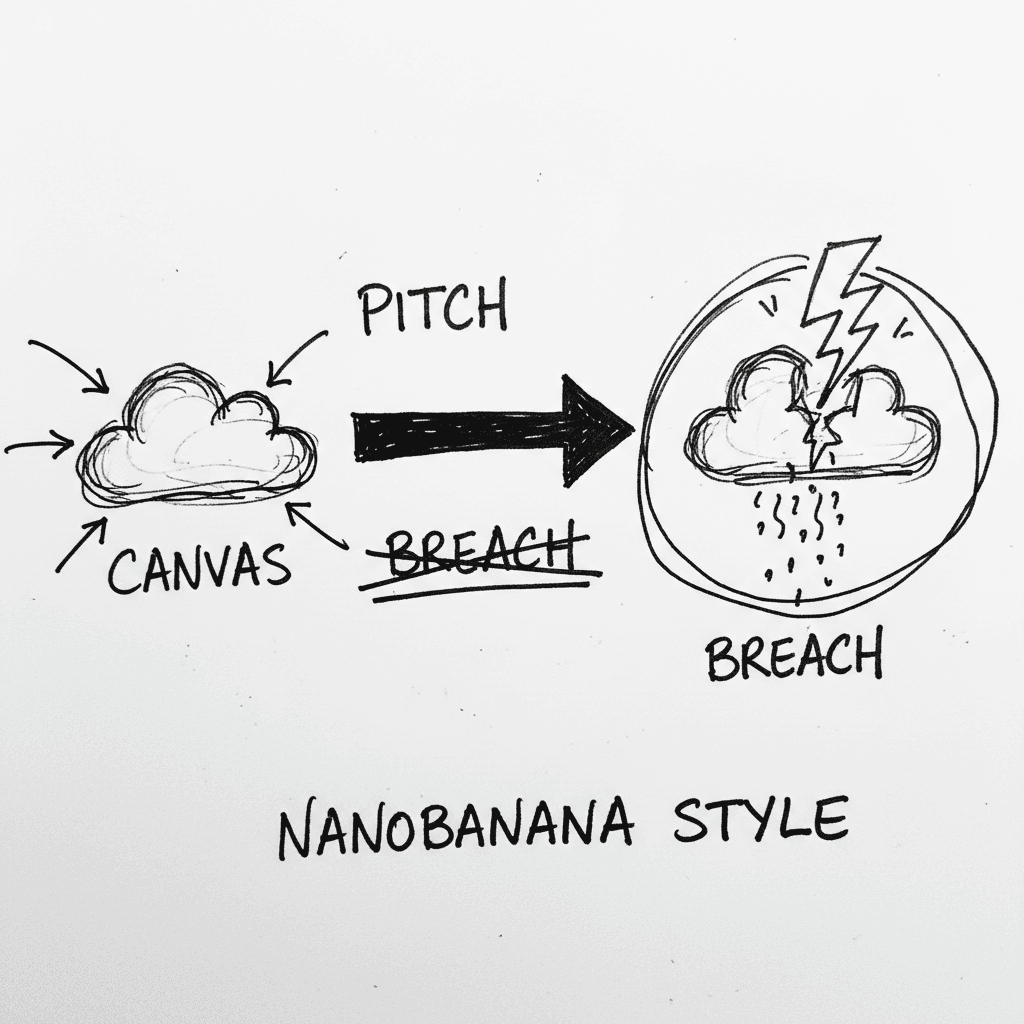
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.