Hardware-Level Surveillance: The Narus STA 6400 and Room 641A
Narus marketed the STA 6400 as a "Semantic Traffic Analyzer" for carrier-grade billing and traffic classification. Mark Klein’s leaked documentation proved it was actually the engine for a "country ta

The Pitch
Narus marketed the STA 6400 as a "Semantic Traffic Analyzer" for carrier-grade billing and traffic classification. Mark Klein’s leaked documentation proved it was actually the engine for a "country tap," allowing the NSA to mirror backbone traffic at the hardware level.
Under the Hood
The system relied on physical fibre-optic splitters installed at AT&T switching hubs, which mirrored 100% of internet traffic into secret, NSA-controlled "black rooms." Mark Klein provided over 100 pages of authenticated AT&T schematics proving this hardware-level intercept was built into the network's core (Source: MIT Press, April 2026).
The Narus STA 6400 analyzed IP packets in real-time, enabling what the NSA termed "Total Situational Awareness." It transformed a standard network management tool into a mass domestic surveillance platform capable of inspecting data at line rate (Source: eWeek/Historical Records).
Congress effectively neutralised any legal accountability for this by granting retroactive immunity to AT&T and other telcos via the 2008 FISA Amendments Act (Source: Wikipedia/Reddit). This set a dangerous precedent for corporate-state collaboration that circumvents judicial oversight.
Recent 2026 reports indicate that intercepted telco data has an "infinite half-life." Encrypted traffic from older leaks, such as the 2019 and 2021 AT&T breaches, is currently being decrypted using modern compute clusters and weaponised (Source: kmsecurity.co.za).
We don't know the current physical status of Room 641A in 2026, as it has likely been virtualised or moved. The exact technical transition from the original STA 6400 hardware to current AI-driven packet inspectors remains a state secret (UsedBy Dossier).
Marcus's Take
Room 641A is the ultimate cautionary tale for backend engineers regarding telemetry and "dual-use" tools. The only thing more efficient than their packet inspection was the speed at which Congress granted them immunity. In 2026, the risk isn't just capture; it’s the persistence of that data, as what was captured years ago is now being cracked by modern AI-enhanced decryption. Assume any traffic passing through a Tier 1 switching hub is effectively public record and act accordingly at the application layer.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
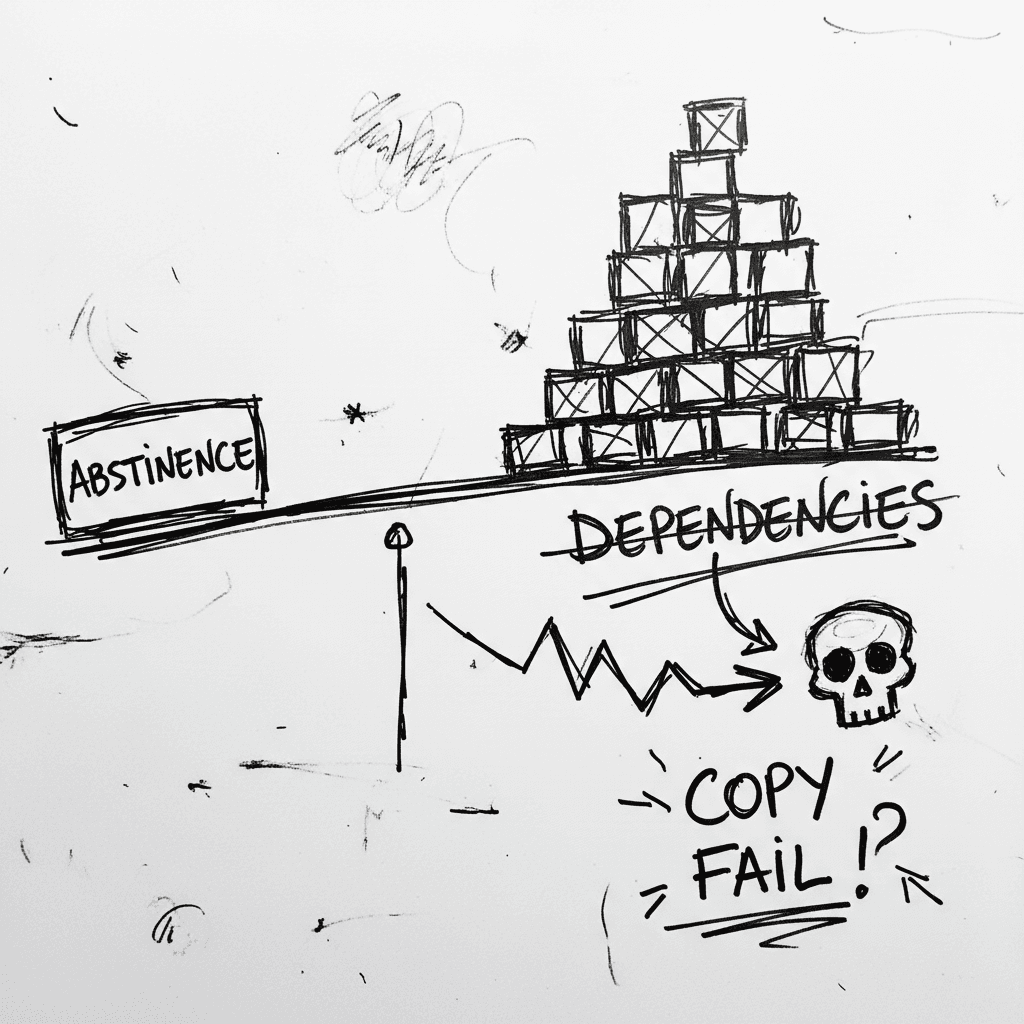
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
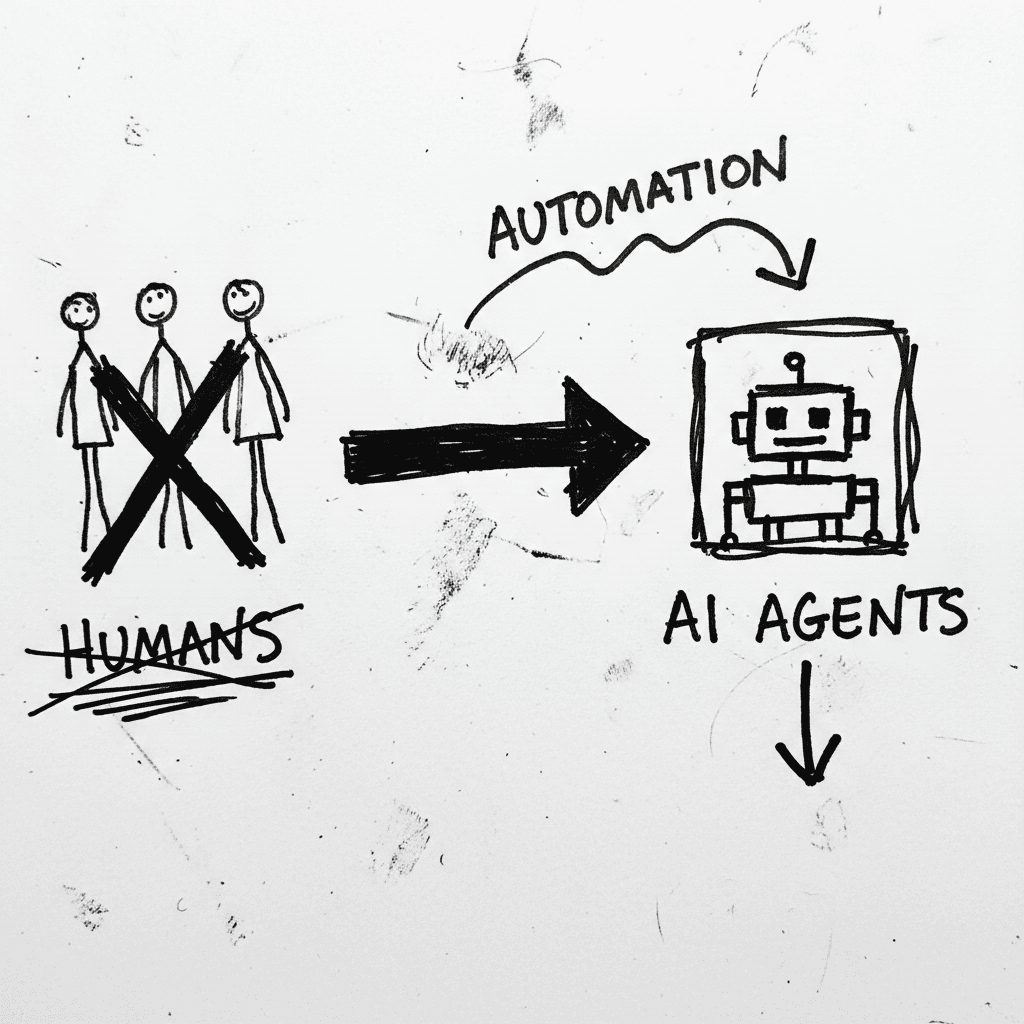
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
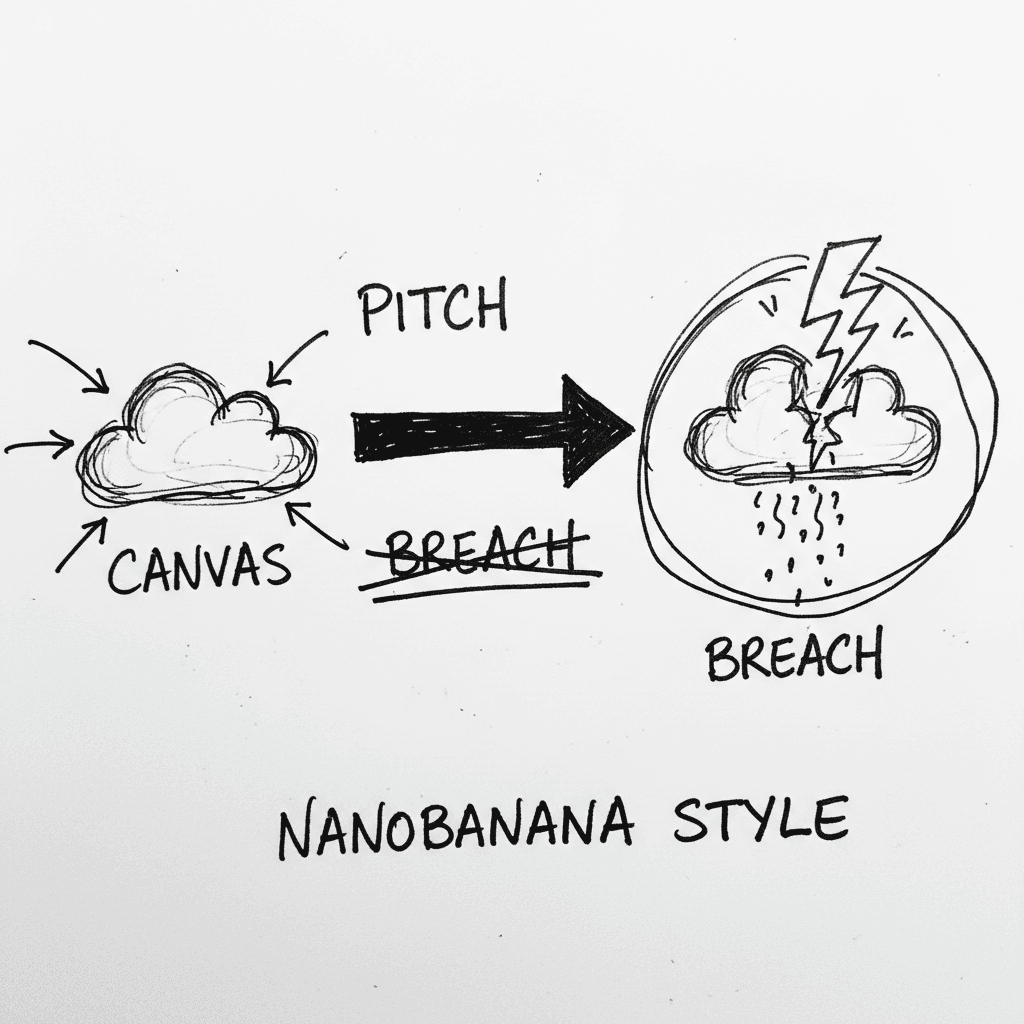
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.