Neutralizing Forty-Year-Old Copy Protection on Legacy RPG Systems
Lead Wikimedia engineer Dmitry Brant has documented a methodology for bypassing parallel port dongles to rescue data from legacy RPG-based accounting software. This approach targets the "industrial de

The Pitch
Lead Wikimedia engineer Dmitry Brant has documented a methodology for bypassing parallel port dongles to rescue data from legacy RPG-based accounting software. This approach targets the "industrial debt" of firms still running systems on hardware that has been out of production for decades. (Source: dmitrybrant.com).
Under the Hood
The process relies on "Software Archaeology" rather than modern brute-force decryption. The target was a hardware key from the defunct Software Security Inc of Stamford, CT. (Source: Patent records). Brant utilized assembly-level patches, specifically flipping conditional jumps (JE/JNE to JMP), to bypass the validation checks in the code. (Source: Blog).
Technical debt remains the primary driver for this research. Hacker News contributors note that civil engineering and accounting firms in 2026 are frequently locked out of critical data when these physical failure points finally break. Replacement parallel port components are non-existent in the current market, necessitating a move to emulation. (Source: HN Comment #4, #5).
Limitations are significant. While binary patching works for 1980s-era tech, modern USB-A and USB-C dongles utilize on-chip encryption. Attempting these patches on current hardware is a waste of cycles. (UsedBy Dossier).
We don't know yet the exact 2026-era emulator configuration used for the Windows 98 environment. Furthermore, the dossier does not specify if AI-assisted decompilers like Claude 4.5 Opus or Claude Code were used for the final patch. (UsedBy Dossier).
Marcus's Take
This isn't a strategy for modern security; it’s a digital rescue mission. If your firm is still relying on a physical dongle from the Thatcher era to access its general ledger, you aren't running a business—you’re running a museum. Use Brant’s methodology to migrate your data to a modern stack immediately, then recycle the hardware. It is the only logical path when your "security" relies on a company that hasn't existed since the nineties.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
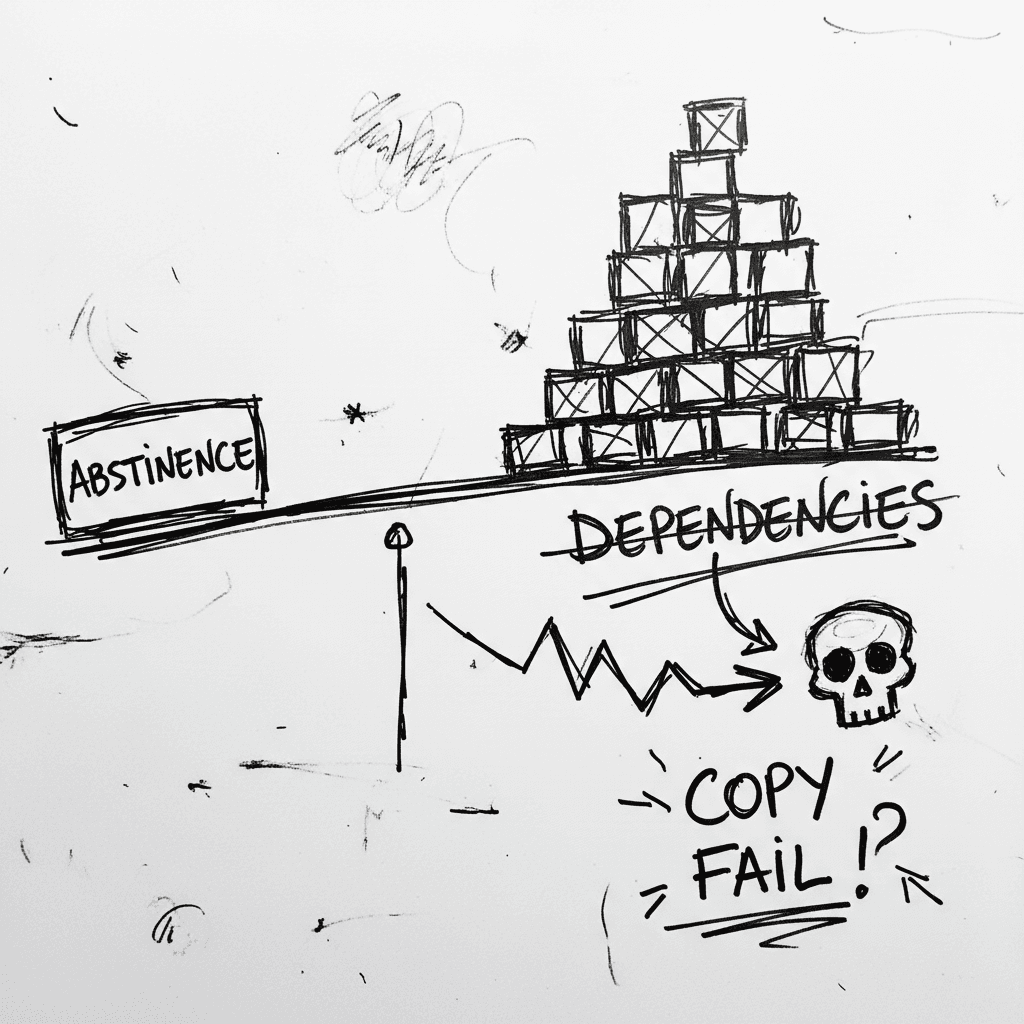
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
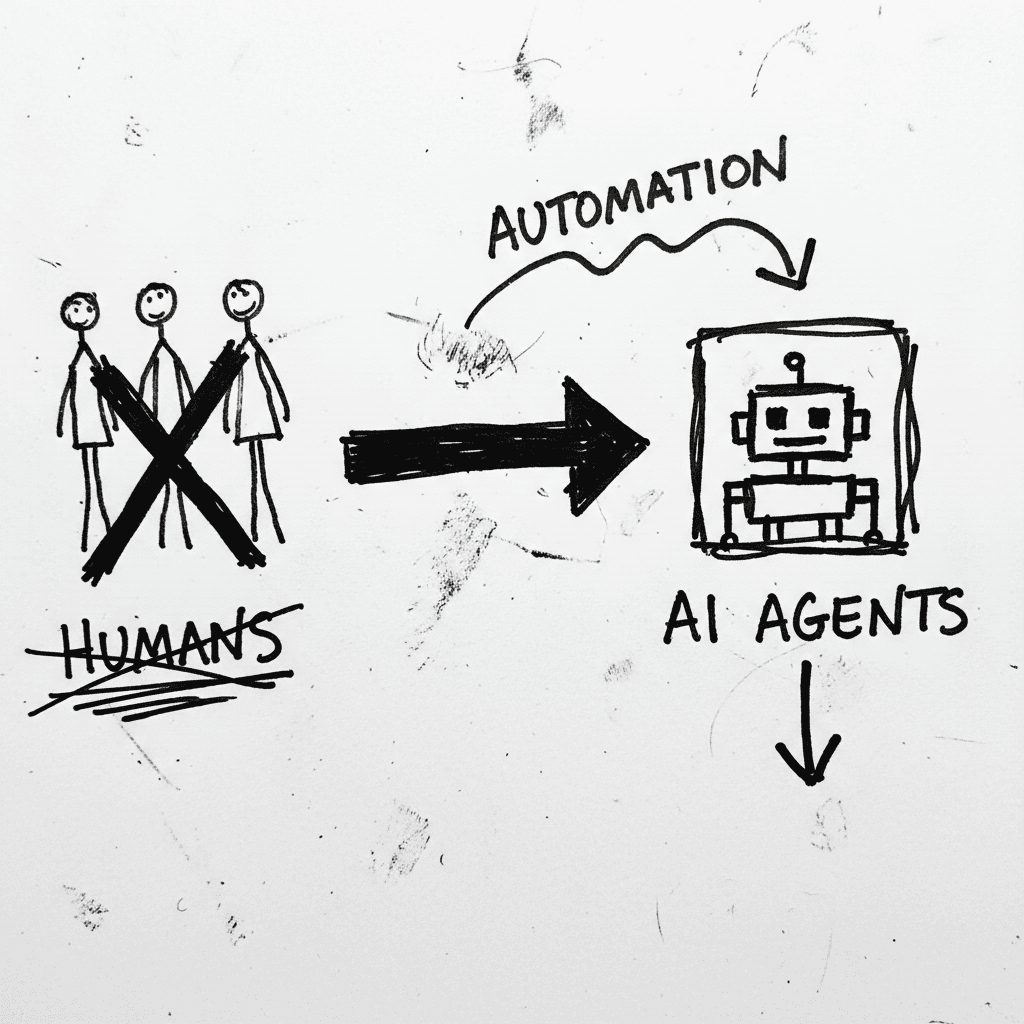
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
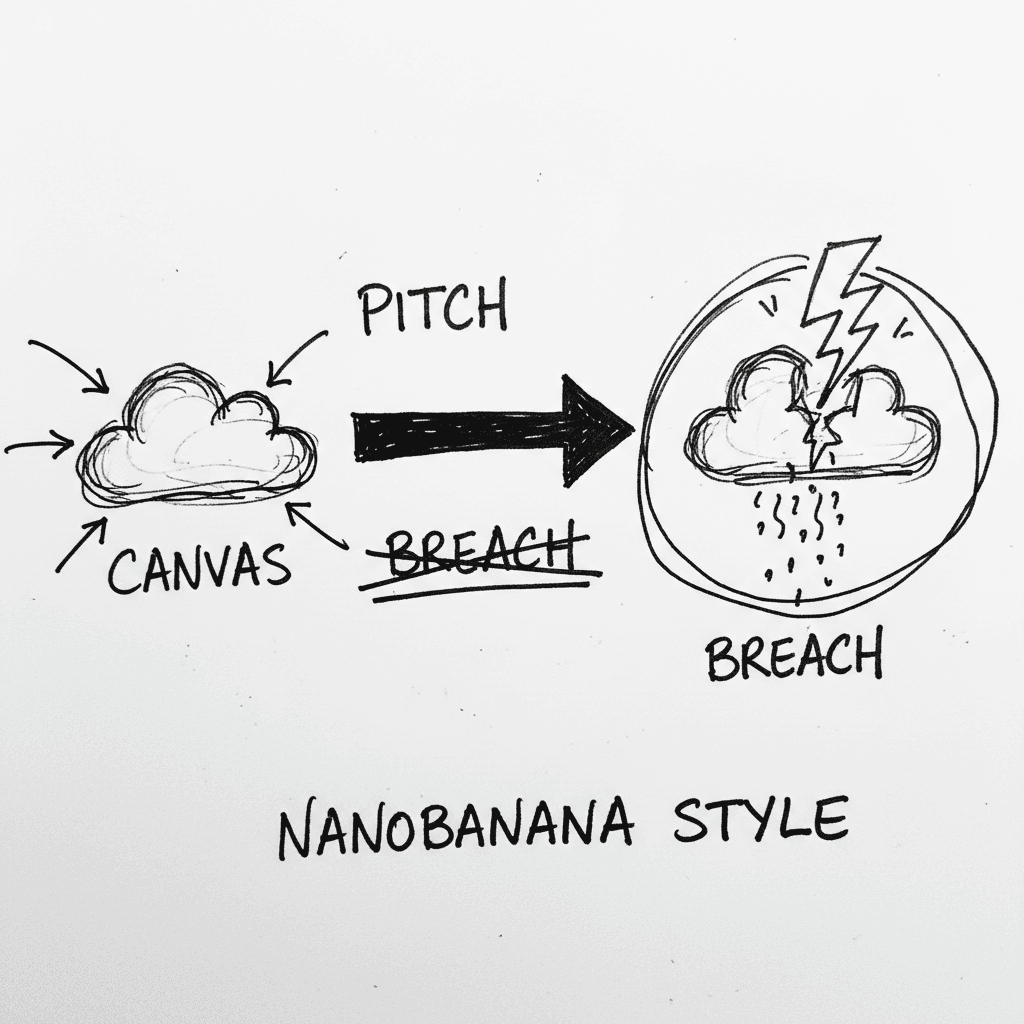
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.