OpenClaw: Local Agentic AI and the Risks of LLM-Controlled RCE
OpenClaw is a self-hosted, MIT-licensed personal assistant designed to bridge LLMs with local shells and 100+ external services like WhatsApp and Gmail (GitHub). It gained over 100,000 GitHub stars in

The Pitch
OpenClaw is a self-hosted, MIT-licensed personal assistant designed to bridge LLMs with local shells and 100+ external services like WhatsApp and Gmail (GitHub). It gained over 100,000 GitHub stars in January 2026 by promising a "real intelligence" agent that operates under user-defined rules rather than corporate guardrails (Forbes). The tool is designed to live directly on a user's machine, providing a persistent automation layer for developers using Claude 4.5 Opus and GPT-5 (MacStories).
Under the Hood
OpenClaw operates as a local orchestration engine utilising Claude 4.5 Opus and GPT-5 to automate tasks across 100+ services, including WhatsApp and the system shell (MacStories).
The project, founded by Peter Steinberger, achieved 100,000 GitHub stars this week but suffered from "handle sniping" by scammers during two rapid rebrands (Malwarebytes).
Sandboxing is currently an "opt-in" feature, meaning the agent has full shell access to the host machine by default, creating a significant Remote Code Execution (RCE) risk (HN).
Researchers found that prompt injection via incoming data can trigger the agent to exfiltrate private information, such as forwarding recent emails to an attacker (DEV.to).
Shodan scans have identified hundreds of OpenClaw control servers that are publicly accessible and leaking plaintext API keys and OAuth secrets (Acuvity).
We don't know yet whether there is venture backing for the project or if a managed "Gateway" service will have public pricing (GitHub).
Marcus's Take
OpenClaw is a textbook case of architectural recklessness masked by high-velocity development. Giving an LLM shell access without mandatory sandboxing is the digital equivalent of leaving your front door open and hoping the local burglars are too busy reading the Terms of Service to notice. The project’s inability to protect its own social handles from handle-sniping scammers further indicates a lack of operational maturity (Malwarebytes). While the integration breadth is useful for hobbyists, deploying this on any machine containing production credentials or personal files is professionally irresponsible. Keep it in a strictly isolated container or stay away entirely.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
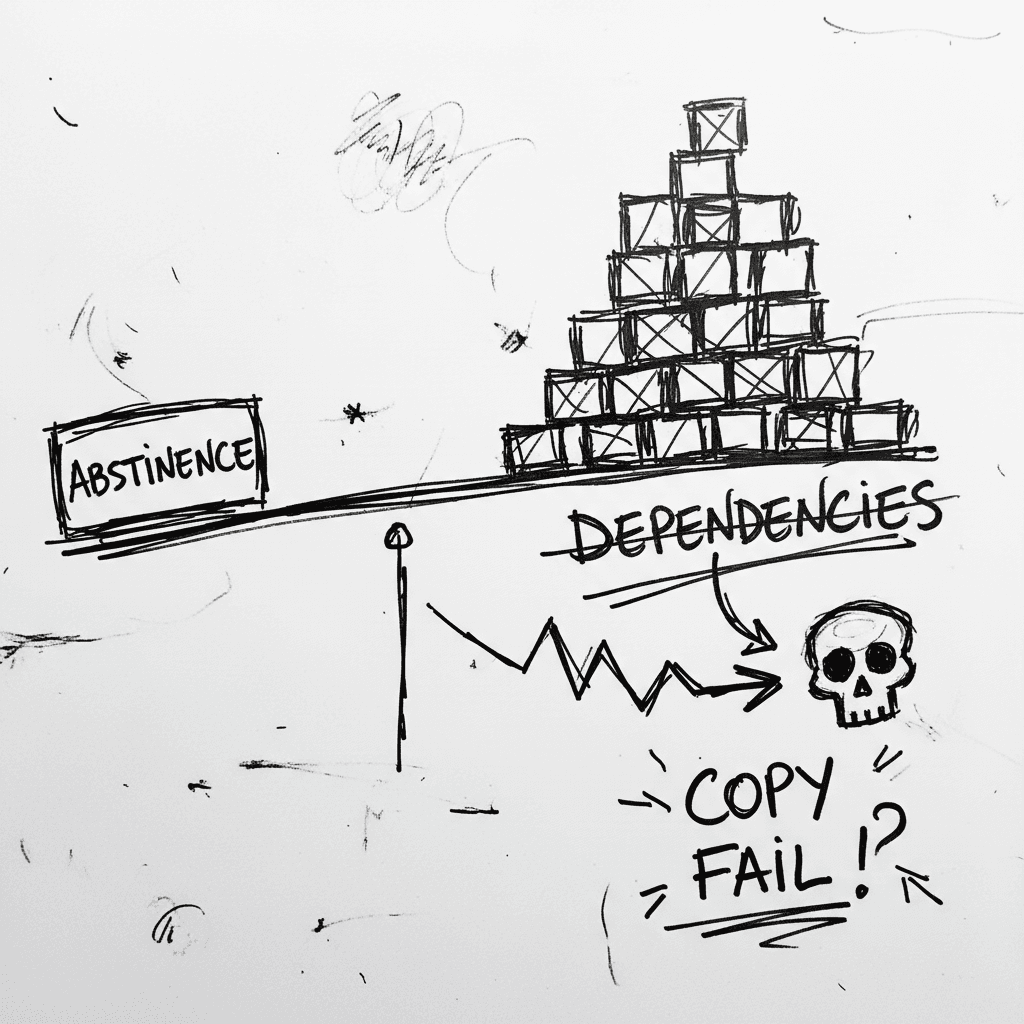
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
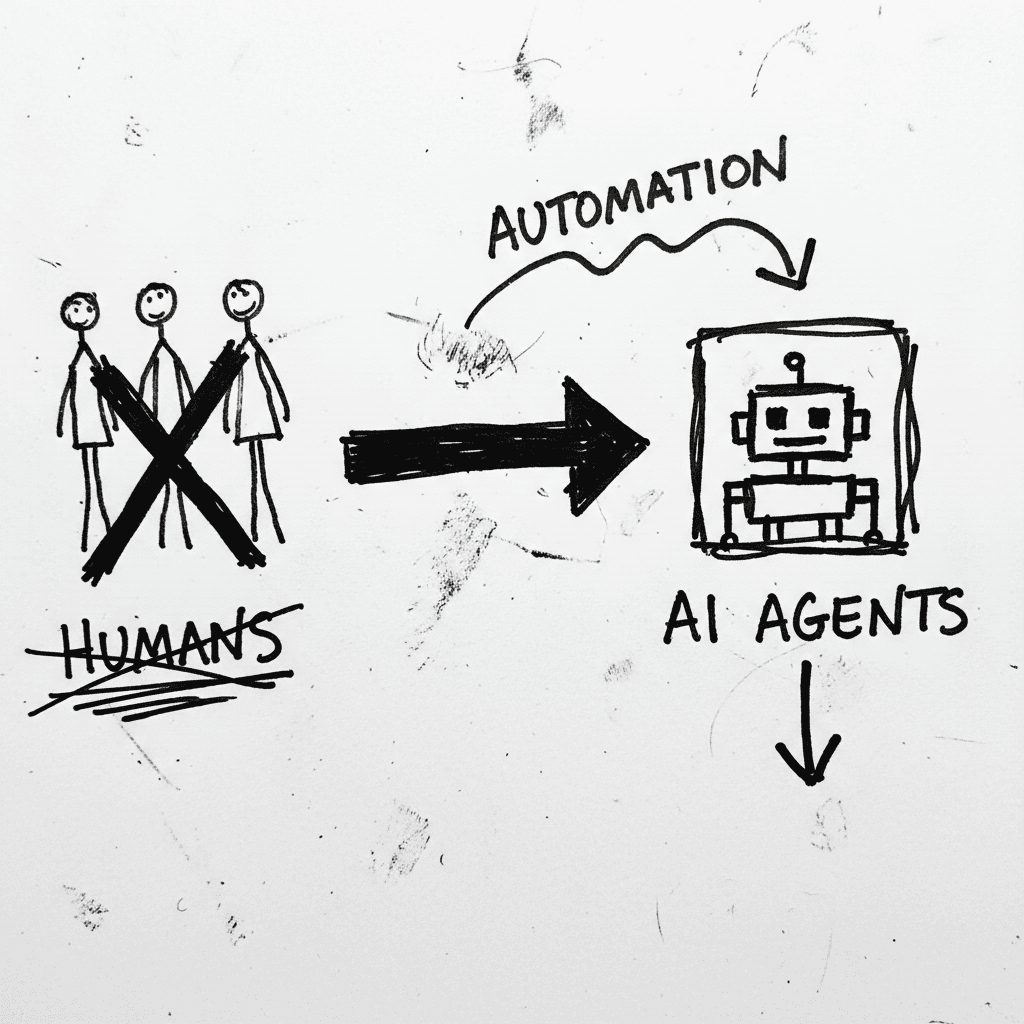
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
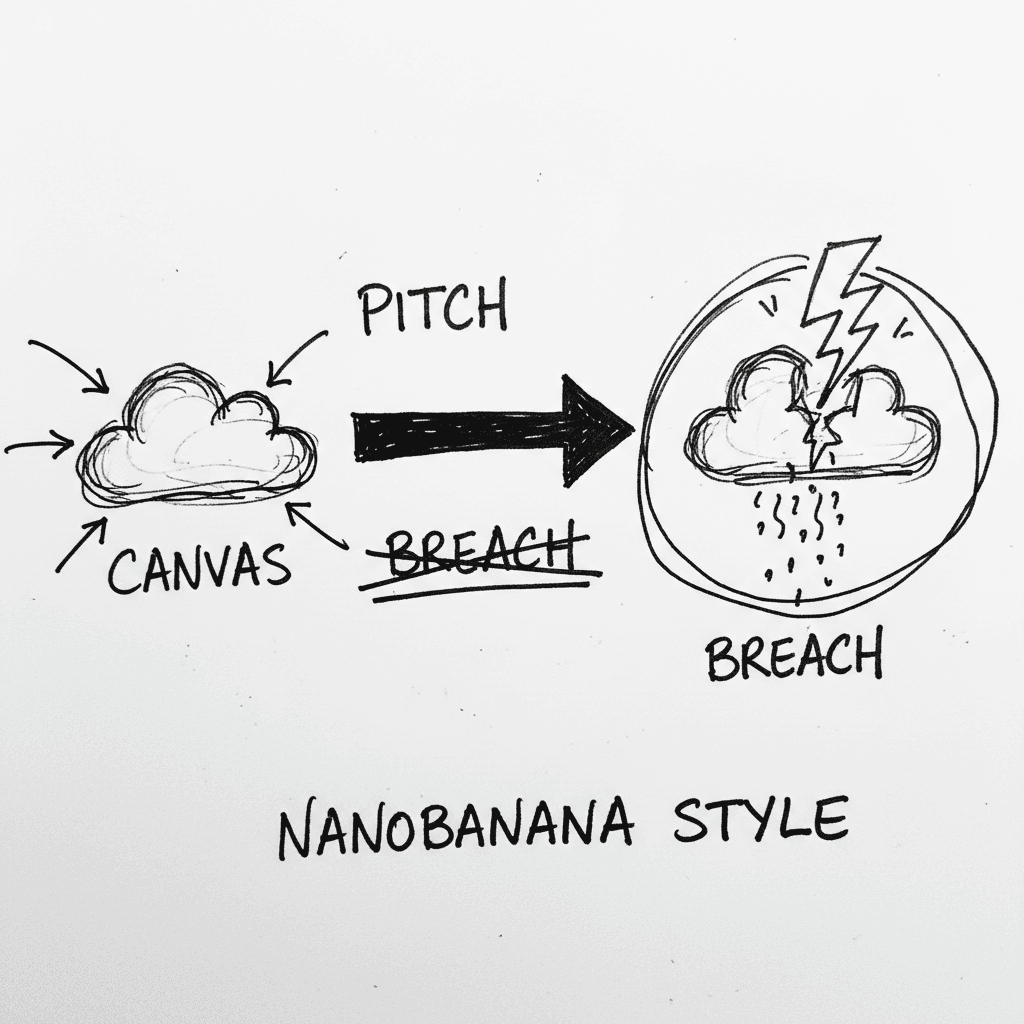
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.