The State of uutils/coreutils in Ubuntu 26.04 LTS
uutils/coreutils is a Rust-based attempt to achieve functional parity with GNU Coreutils while providing a memory-safe alternative. While it is now the default for 80 utilities in the current Ubuntu 2

The Pitch
uutils/coreutils is a Rust-based attempt to achieve functional parity with GNU Coreutils while providing a memory-safe alternative. While it is now the default for 80 utilities in the current Ubuntu 26.04 LTS release, it remains a partial implementation due to persistent logic concerns (computingforgeeks.com, April 2026).
Under the Hood
Functional parity currently sits at 94.74%, with 630 of 665 GNU tests passing as of this month (ostechnix.com, April 2026). Performance benchmarks show substantial advantages for specific workloads; uu-sort outperformed the legacy GNU implementation by nearly 30x when processing large-scale logs in recent tests (makeuseof.com, February 2026).
However, a Zellic security audit identified 113 total issues, including 44 CVEs related to logic errors and TOCTOU (Time-of-Check to Time-of-Use) races (Ubuntu Discourse, April 2026). One specific flaw, CVE-2026-35369, highlighted incorrect behavior in the kill -1 command (UsedBy Dossier).
Canonical has explicitly excluded cp, mv, and rm from the default uutils migration. These critical commands are still handled by GNU to avoid data destruction risks associated with 8 unresolved filesystem-altering race conditions (Ubuntu Foundation, April 2026).
Data integrity issues persist due to strict UTF-8 enforcement. Commands like comm and ln may silently corrupt filenames that are stored as raw bytes rather than valid UTF-8, which GNU handles correctly (Corrode.dev, April 2026).
The dependency tree is also a point of concern for backend architects. While GNU coreutils relies almost exclusively on glibc, uutils pulls in roughly 50 external crates, expanding the potential supply chain attack surface (Zellic Audit Report, 2026).
We don't know yet when the openat API will be stabilized in the Rust Standard Library. Consequently, uutils continues to rely on the rustix crate as a workaround for low-level filesystem access (UsedBy Dossier).
Marcus's Take
You should not swap your core filesystem utilities for uutils on production servers just yet. The memory safety of Rust is a net positive, but it cannot fix fundamental logic errors or race conditions in rm and mv that lead to data loss. Use the Rust implementation for high-throughput pipes where uu-sort provides a clear performance edge, but keep the GNU holdouts for anything that actually writes to the disk. It turns out that "rewrite-it-in-Rust" is a strategy, not a cure for forty years of edge-case logic.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
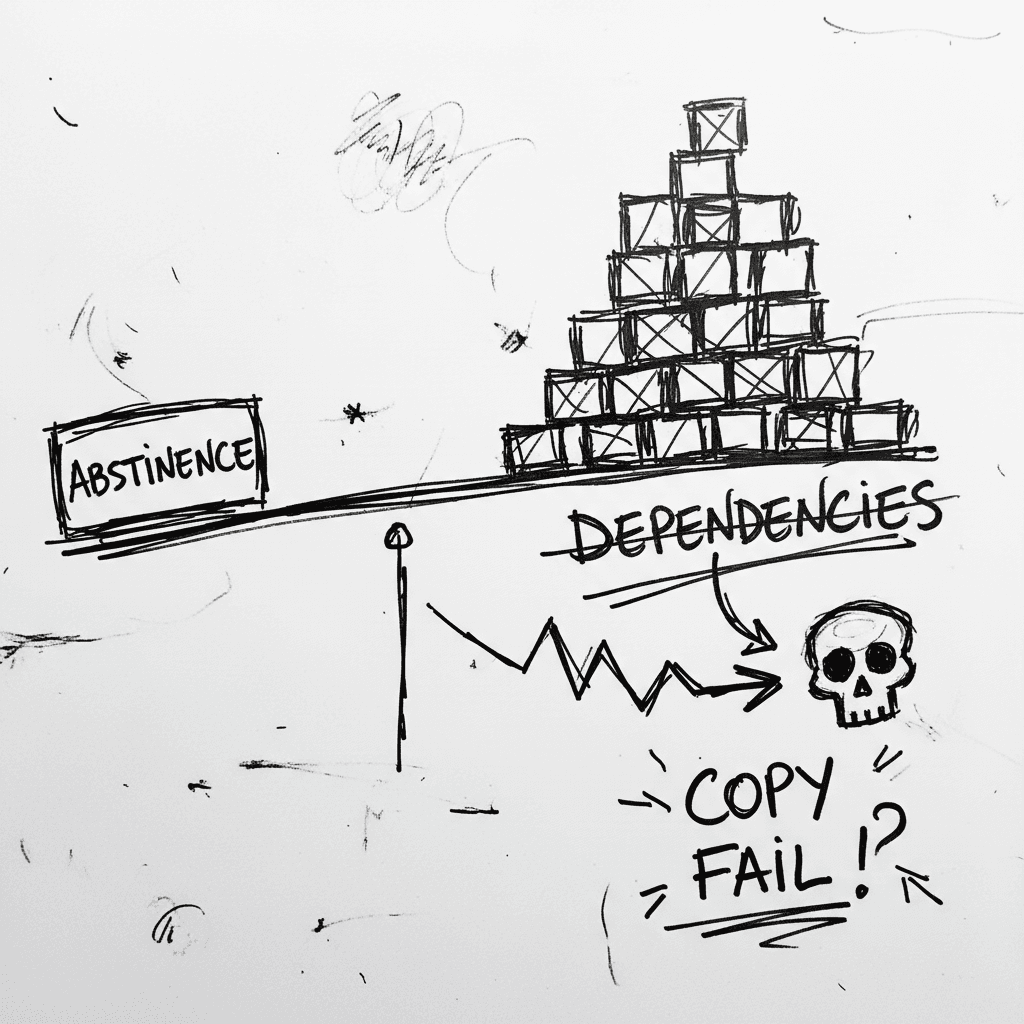
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
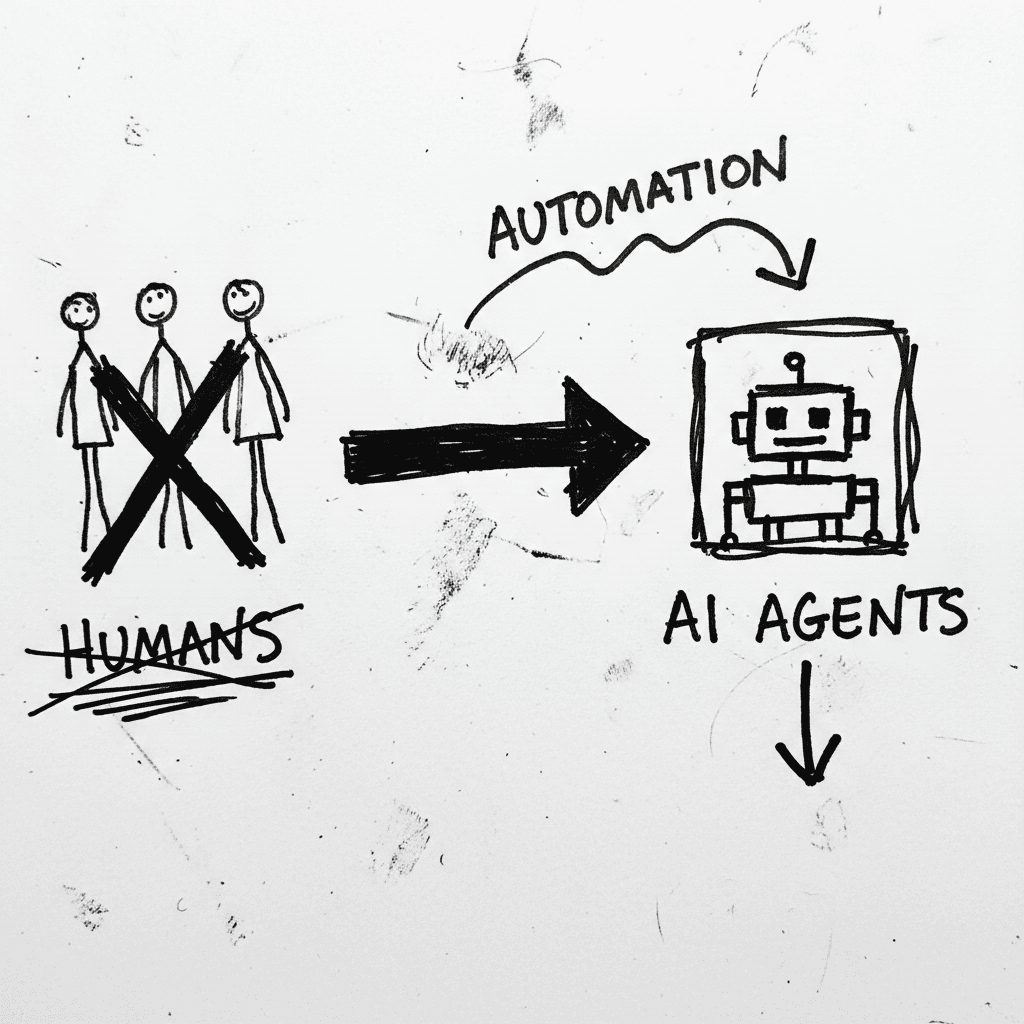
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
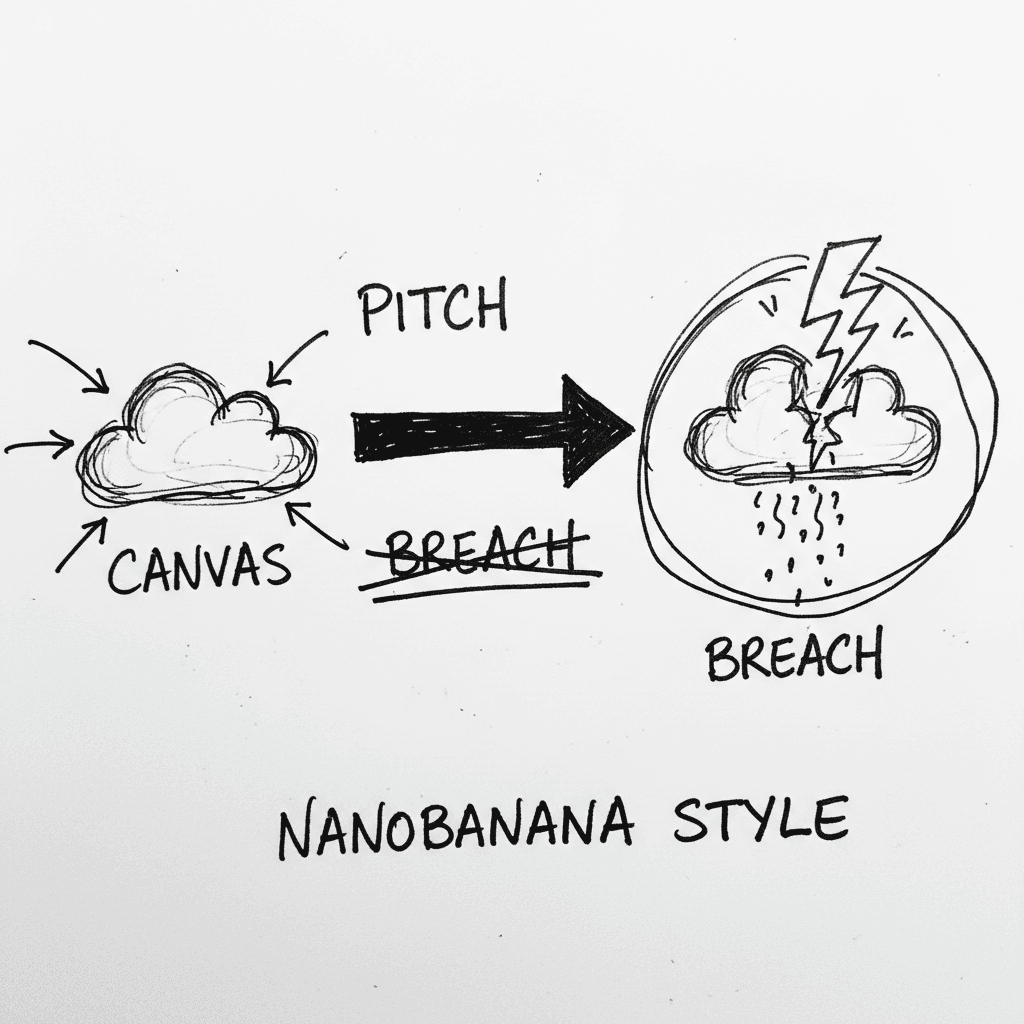
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.