The Technical Failure of Mandatory Age Verification Infrastructure
Australia’s mandatory age verification for social media platforms became enforceable on December 10, 2025, triggering a massive shift in how identity is brokered at the application layer (Source: HN T

The Pitch
Australia’s mandatory age verification for social media platforms became enforceable on December 10, 2025, triggering a massive shift in how identity is brokered at the application layer (Source: HN Thread/Spectrum). Governments are forcing platforms to integrate biometric or identity-linked data to gatekeep users under 16, creating a new, high-stakes infrastructure requirement for backend teams.
Under the Hood
The most functional implementation currently relies on European eIDAS 2.0 identity wallets, which utilize Zero-Knowledge Proofs (ZKPs) to verify "over 18" status (Source: HN Comment). This approach allows a user to prove they meet an age threshold without transmitting their actual date of birth or full identity to the requesting service.
However, outside the EU, the reality is a fragmented mess of third-party identity aggregators. These systems consolidate sensitive biometric data into a few high-risk silos, creating what is effectively a honeypot for hackers (Source: IEEE Spectrum). The technical overhead of managing these integrations is non-trivial, and the security implications of storing or even proxying this data are severe.
Despite the 4.7 million account deactivations recorded in Australia since December 2025, the legislation has largely failed to curb minor activity (Source: HN Comment). Users are simply migrating to "ghost accounts" or unmonitored decentralized platforms, often using GPT-5 driven social engineering to bypass automated age-gating (Source: IEEE Spectrum).
The surge in VPN usage to bypass geo-fencing has rendered regional IP-based blocking obsolete. We are seeing an escalation where minors use stolen credentials or AI-generated synthetic identities to satisfy the verification prompts. It is the classic security arms race, but with the state mandating a technical barrier that is fundamentally easy to circumvent.
We don't know yet what the specific success rate of ZKP-based verification looks like in non-EU jurisdictions (UsedBy Dossier). Furthermore, the current liability status of parents whose children use stolen credentials to access restricted services isn't public, leaving a significant legal void for platform operators (UsedBy Dossier).
Marcus's Take
Building centralized identity silos for age verification is an architectural disaster waiting for a data breach. The Australian data proves that mandatory verification doesn't stop minors; it just moves them to less secure, unmonitored environments. If you are forced to implement this, your only ethical and technical choice is ZKP-based identity wallets to avoid the liability of holding PII. Otherwise, skip the centralized biometric approach entirely—it’s a surveillance trap that offers zero real security.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
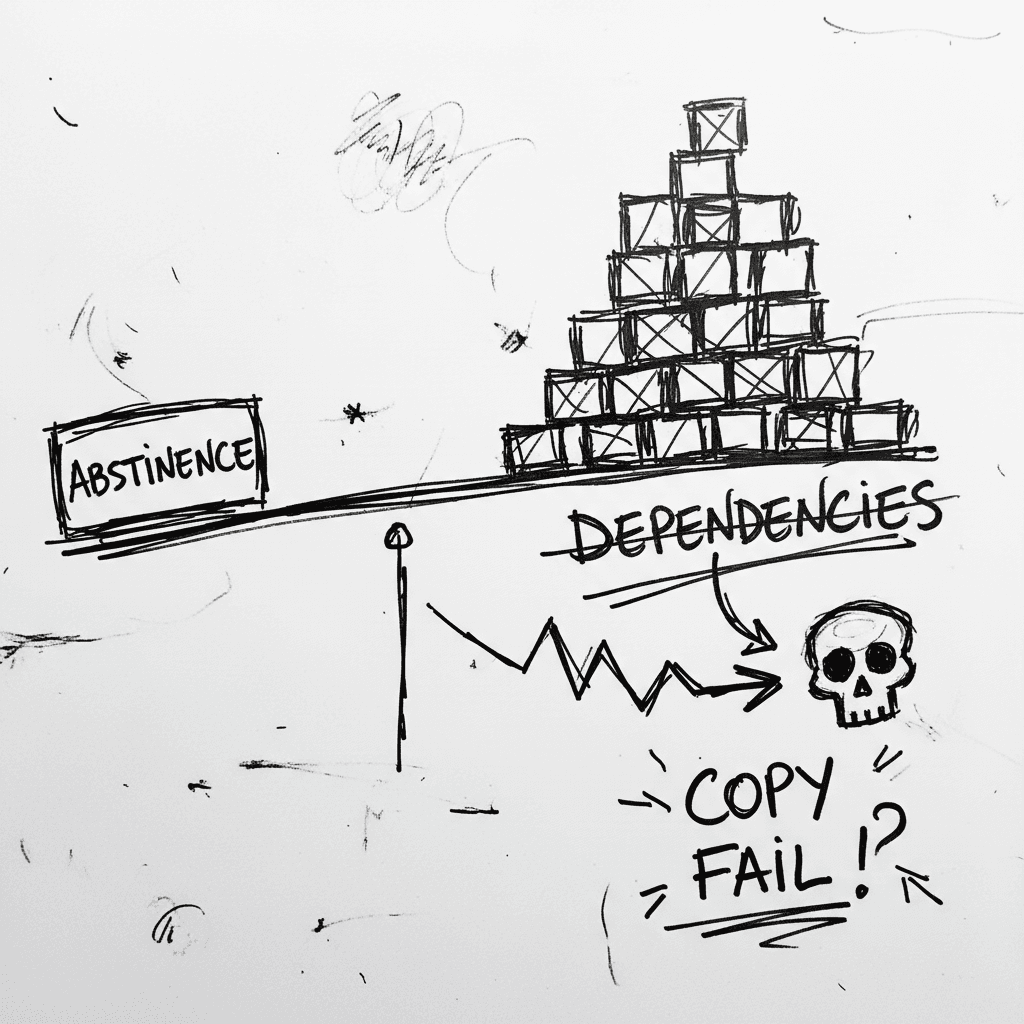
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
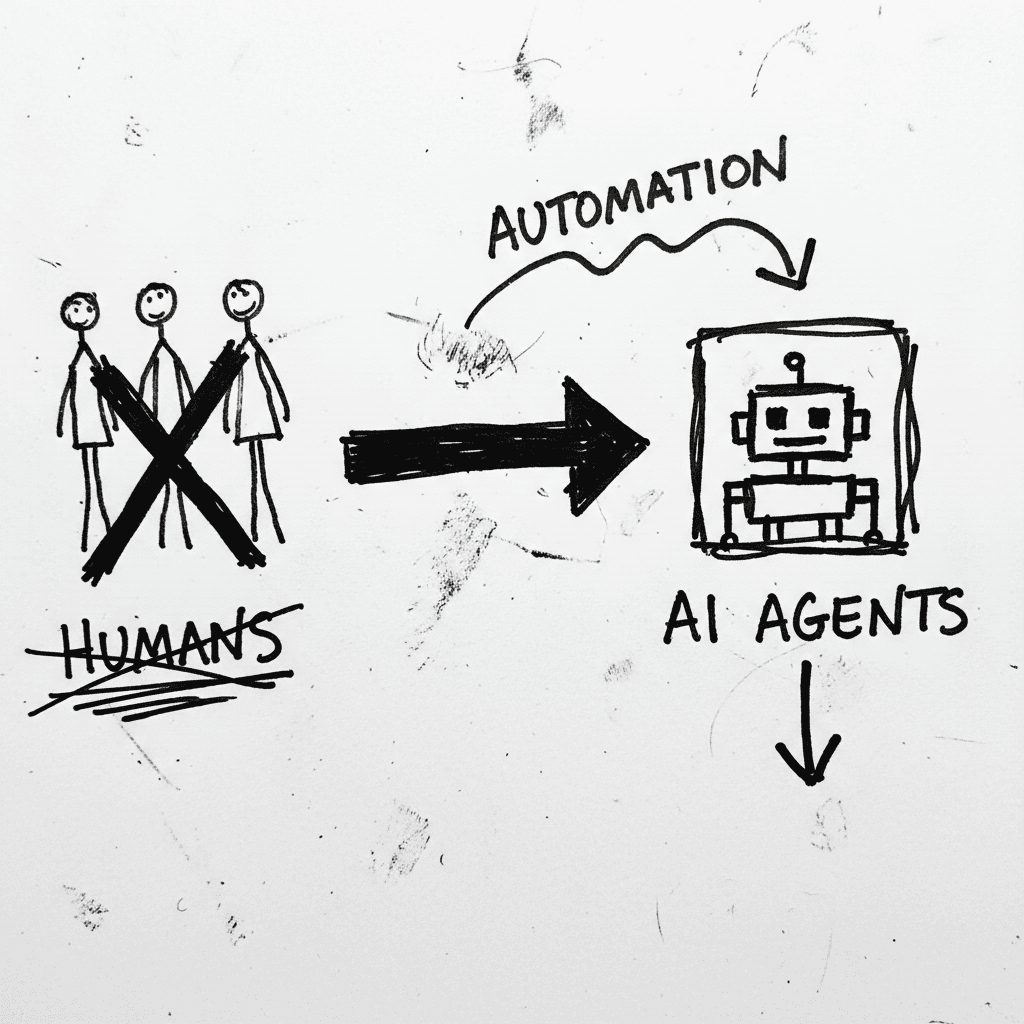
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
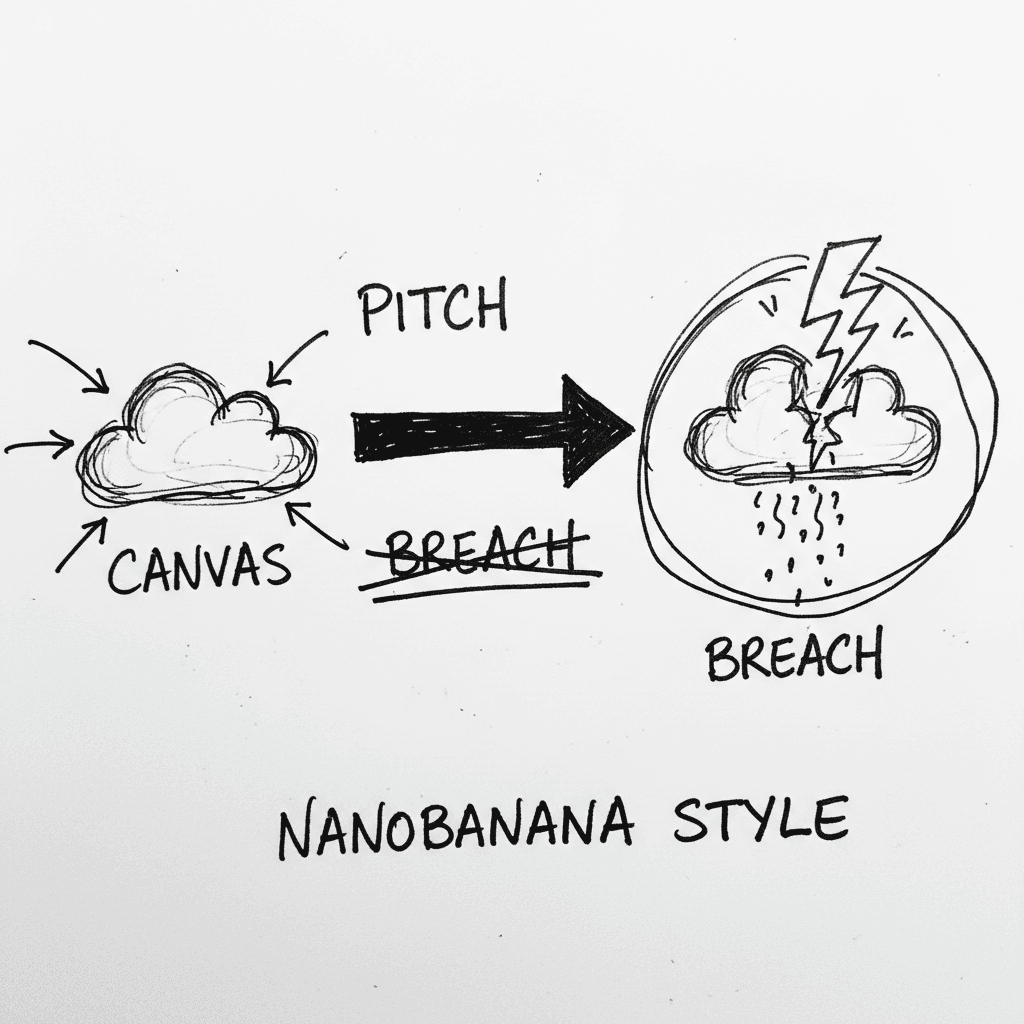
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.