Kernel-Level Isolation for AI Agents: A Review of Agent Safehouse
Agent Safehouse uses the macOS kernel-level "Seatbelt" framework to isolate local AI agents from the host filesystem. It attempts to solve the security risks inherent in giving models like Claude 4.5

The Pitch
Agent Safehouse uses the macOS kernel-level "Seatbelt" framework to isolate local AI agents from the host filesystem. It attempts to solve the security risks inherent in giving models like Claude 4.5 Opus or Claude 4 Sonnet direct shell access by enforcing a strict "deny-first" policy (Source: agent-safehouse.dev). This approach aims to prevent accidental data exfiltration or destructive commands during local agent execution.
Under the Hood
The implementation is a bash-based wrapper currently hosted on GitHub that generates specialized sandbox profiles (Source: github.com). By leveraging sandbox-exec, Safehouse provides a more resilient boundary than application-layer guardrails, which are often susceptible to prompt injection. It is designed specifically for the 2026 "Claw" agent ecosystem (Source: HN Thread/Docs).
However, this isolation comes with significant operational friction. The default policy hides essential global configuration files, such as ~/.gitconfig and SSH keys, from the agent. Restoring functionality requires manual "append-profile" configurations, which can slow down initial deployment (Source: HN Comment).
The sandbox also restricts low-level system interactions necessary for complex development. Tools like pkill and the lldb debugger are blocked by default, preventing agents from managing or inspecting local processes (Source: HN Comment). Furthermore, browser automation via Playwright or headless Chrome is currently reported as unstable within the sandbox environment (Source: HN Comment).
We don't know yet what the specific performance overhead is when wrapping heavy inference tasks in multiple Seatbelt layers, as official benchmarks are missing (UsedBy Dossier). Additionally, while filesystem access is restricted, robust network egress filtering and protection against memory-based credential theft are not yet fully mature (Source: Moltbook).
Marcus's Take
Skip this for complex engineering workflows, but use it for isolated script execution. Agent Safehouse is a necessary response to the "ClawHavoc" security concerns of early 2026, but it currently turns a sophisticated agent into a lobotomized one when asked to interact with a standard dev stack. It is essentially a digital straitjacket—excellent for safety, but try writing production code while wearing one. Wait for better process debugging support before making this your default local wrapper.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
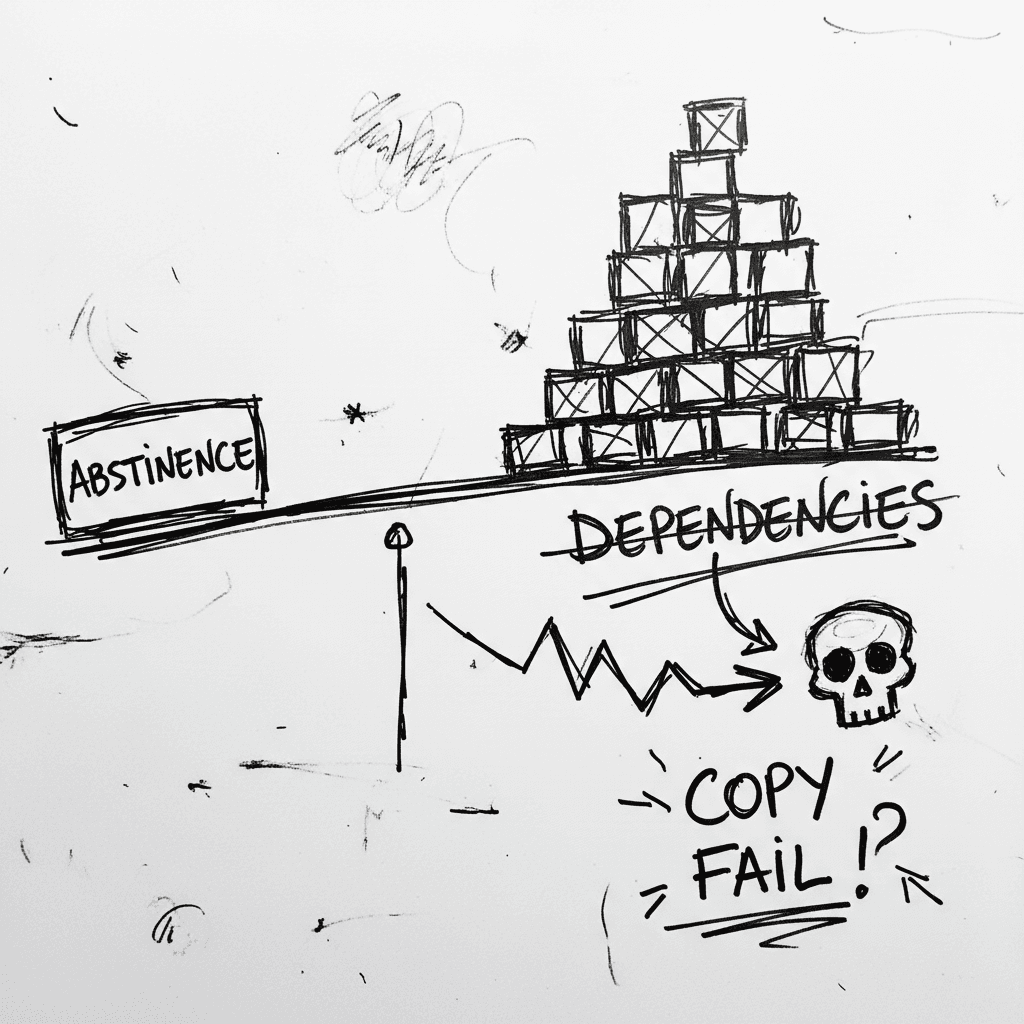
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
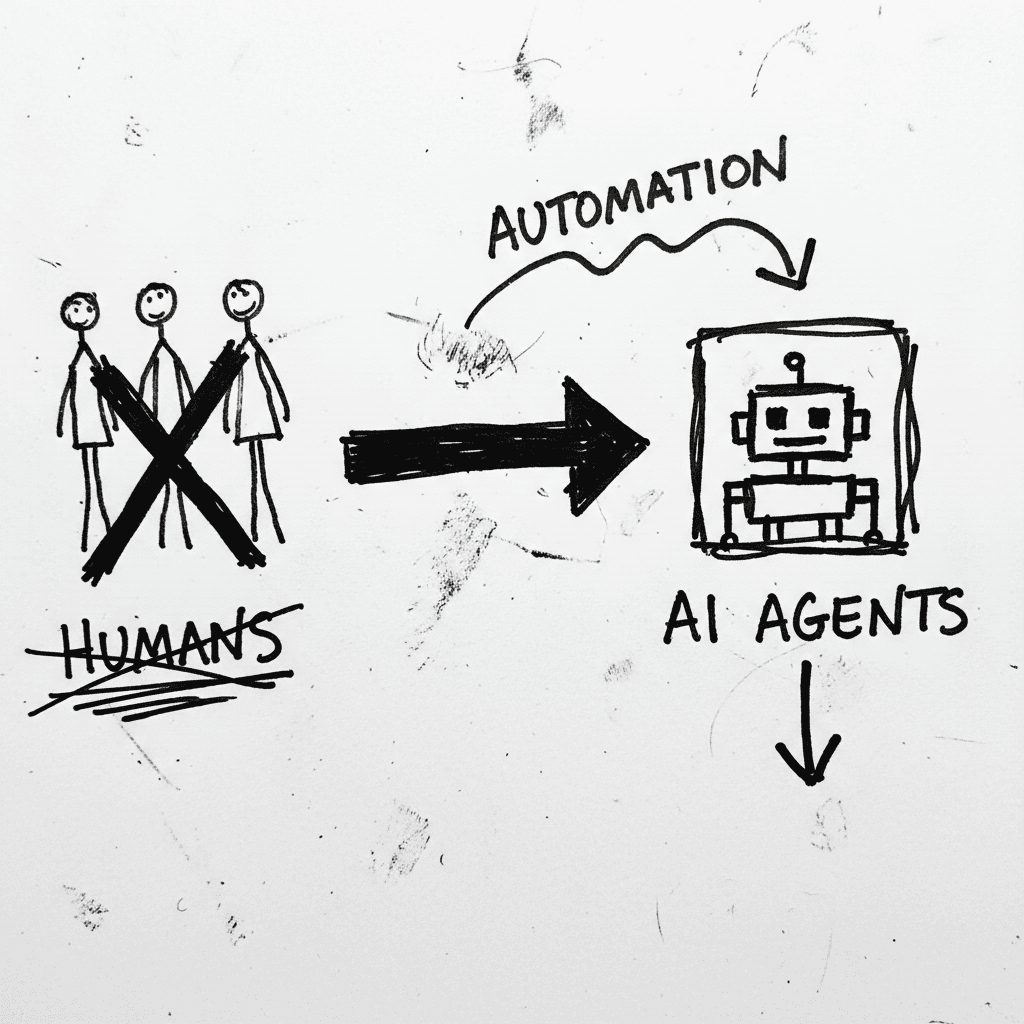
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.