Synology DSM Hostname Leakage via Client-Side Sentry Integration
Synology’s DiskStation Manager (DSM) is currently under scrutiny following reports that its web UI leaks internal hostnames to external monitoring endpoints. Despite marketing these devices as "privat

The Pitch
Synology’s DiskStation Manager (DSM) is currently under scrutiny following reports that its web UI leaks internal hostnames to external monitoring endpoints. Despite marketing these devices as "private clouds" where data remains under physical user control, client-side telemetry is actively bridging the gap between isolated local networks and third-party SaaS providers. (UsedBy Dossier)
Under the Hood
Synology DSM’s web interface is leaking internal FQDNs and network metadata to third-party Sentry endpoints via client-side telemetry polling. (rachelbythebay.com)
The leak is triggered by client-side traces embedded in the UI that call home to external monitoring endpoints. (Hacker News)
While administrators use wildcard SSL certificates to prevent hostname leakage in public Certificate Transparency logs, application-layer logging captures the full request URL. (rachelbythebay.com)
Telemetry is being sent to GCP-hosted instances during standard UI usage, often without explicit user realization. (rachelbythebay.com)
Internal hostnames captured in these logs often contain sensitive business data, such as internal project codenames or merger details. (Hacker News)
We don't know yet if there is a verified way to fully opt-out of these client-side Sentry reports within the DSM settings. (UsedBy Dossier)
It is also currently unknown if other prosumer brands like QNAP or TrueNAS are utilizing similar monitoring stacks that exhibit this behavior. (UsedBy Dossier)
Marcus's Take
The "private cloud" label is increasingly becoming a marketing fiction as manufacturers prioritize their own observability over user privacy. If your internal hostnames contain sensitive project data—which they shouldn't, but let's be honest, they do—you are leaking your roadmap to external cloud hosts. For any production environment requiring genuine isolation, DSM is no longer a "set and forget" solution. You must now implement aggressive egress filtering or DNS sinkholing to kill these telemetry calls; if you aren't controlling the outbound traffic, you don't actually own the box.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
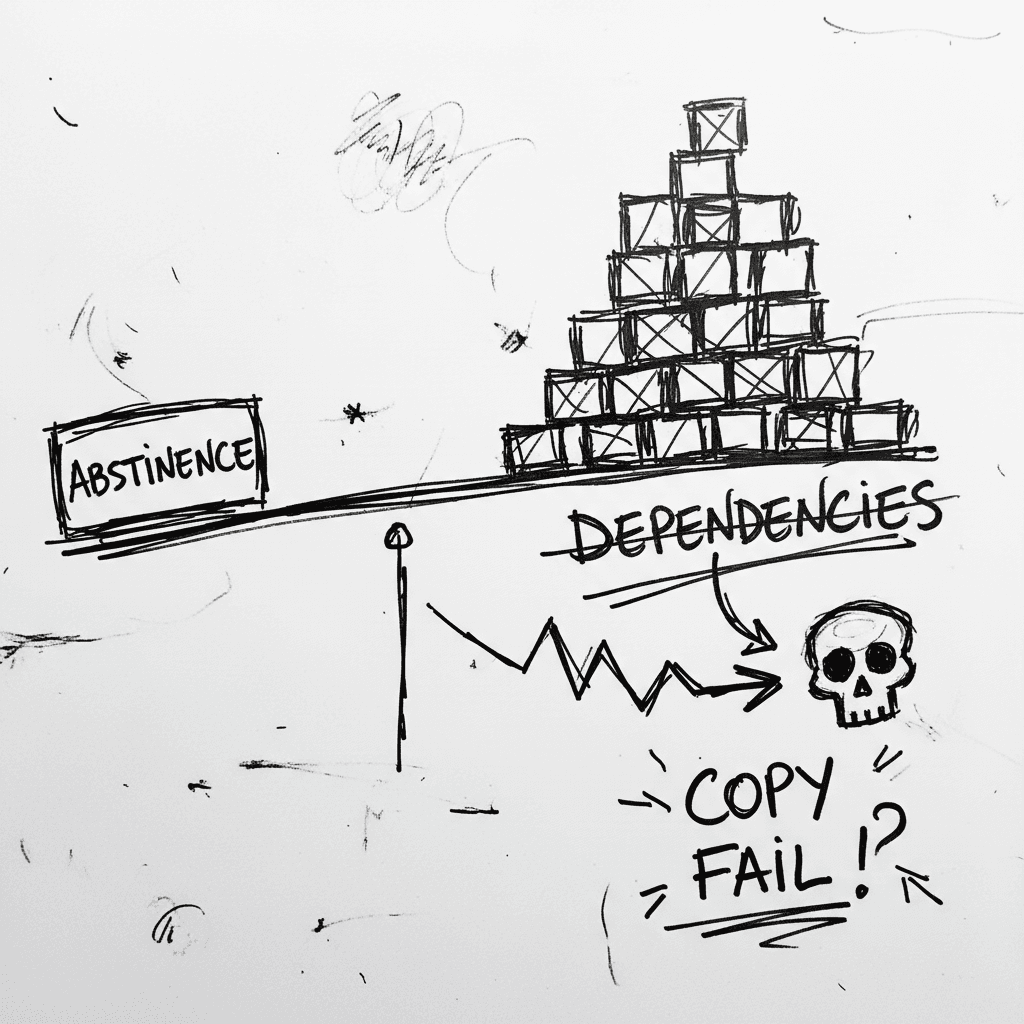
The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe
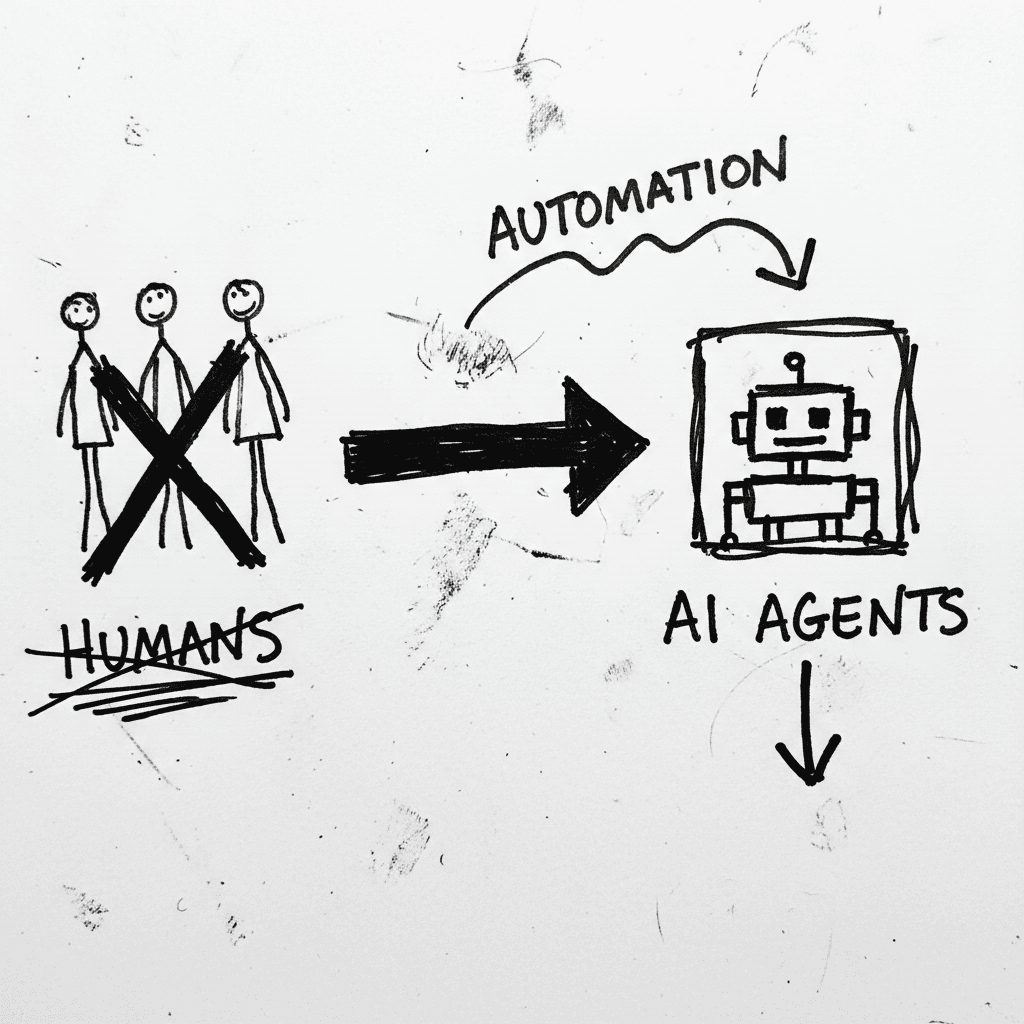
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
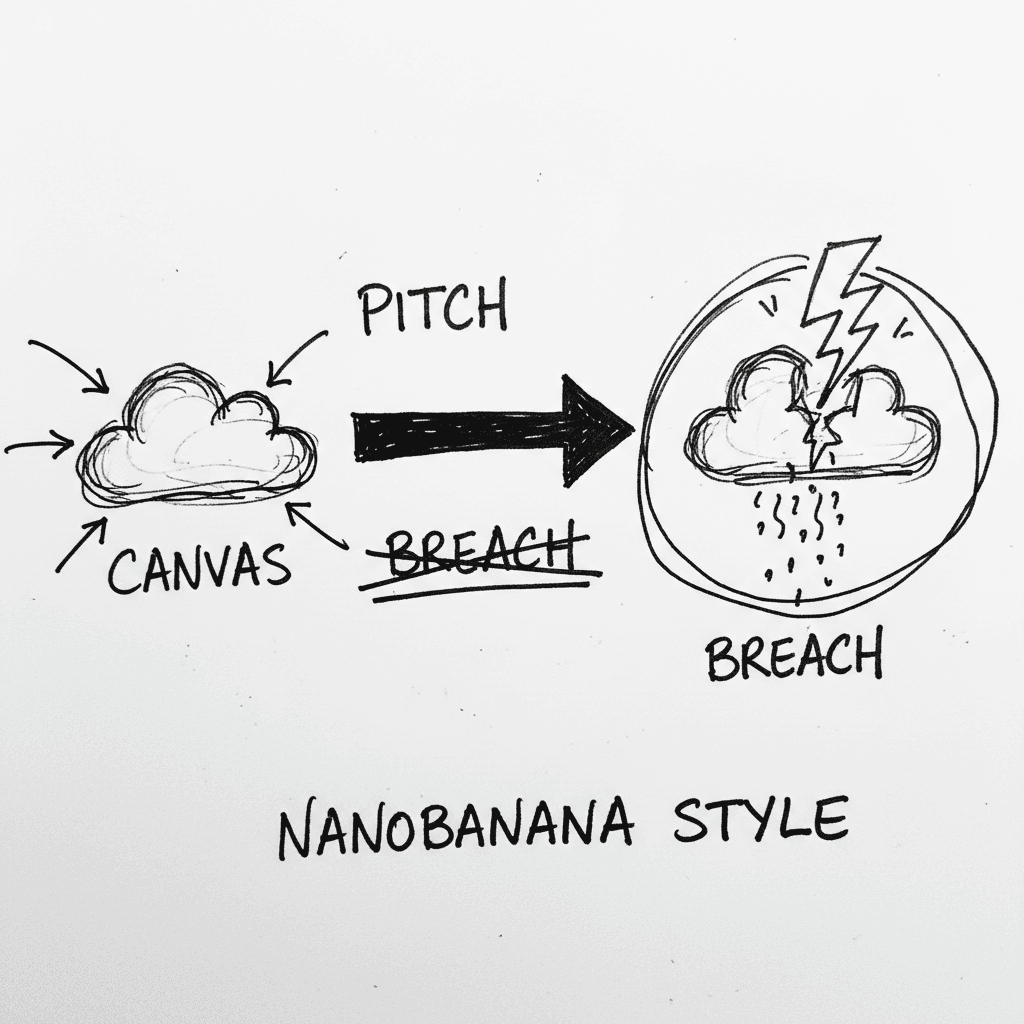
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.